Knowledge Byte: Top 9 Cloud Computing Threats

Cloud Credential Council (CCC)

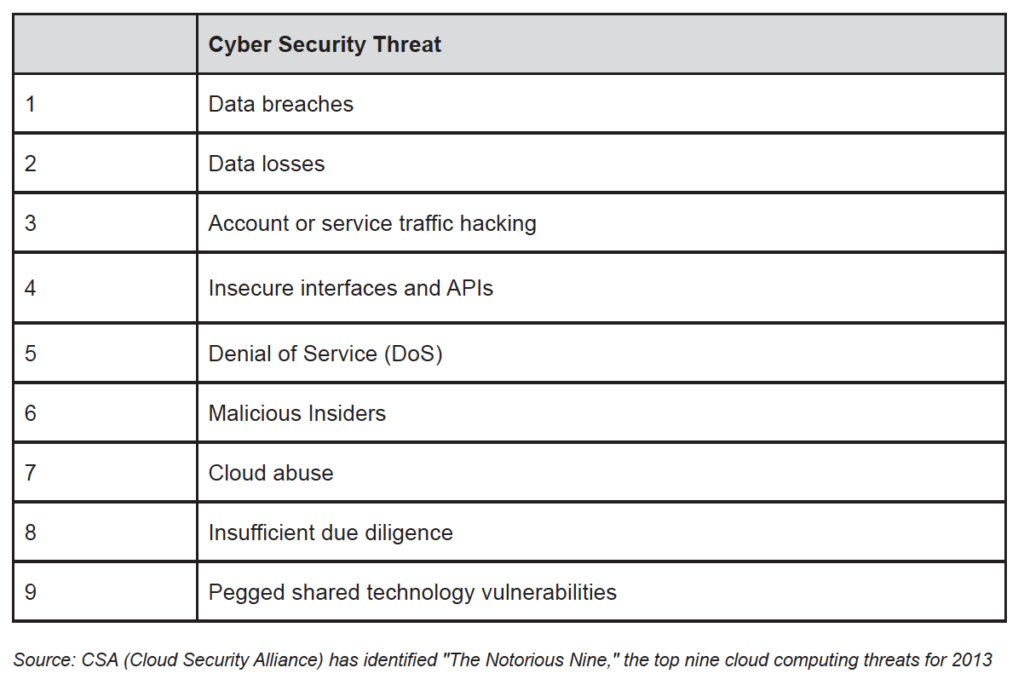
Back in 2013, the Cloud Security Alliance (CSA) identified “The Notorious Nine,” the top nine cloud computing threats.
Data Breaches
Cloud computing has introduced new avenues of attack on an organization’s confidential data. If a multi-tenant cloud service database is not properly designed, a flaw in one client’s application could allow an attacker access not only to that client’s data but every other client’s data as well.
Data Losses
Data loss refers to the loss of data through accidental deletion or natural disasters such as fire or flood. Data can also be deleted by a malicious hacker. Issues regarding data loss can also occur in the need to record data for audit purposes, such as HIPPA compliance, where a data loss would violate the rules.
Account or Service Traffic Hacking
If an attacker gains access to your credentials, he or she can eavesdrop on your activities and transactions, manipulate data, return falsified information, and redirect your clients to illegitimate websites.
Insecure Interfaces and APIs
IT admins rely on interfaces for cloud provisioning, management, orchestration, and monitoring. APIs are integral to the security and availability of general cloud services. Consumer organizations and third parties are known to build on these interfaces, injecting add-on services. This introduces the complexity of the new layered API and increases risk, as organizations may be required to relinquish their credentials to third parties in order to enable their agency.
Denial of Service (DoS)
DoS has been an Internet threat for years, but it becomes more problematic in the age of cloud computing when organizations are dependent on the 24/7 availability of one or more services. DoS outages can be costly for customers who are billed based on compute cycles and disk space consumed. While an attacker may not succeed in knocking out a service entirely, he or she may cause a delay in processing time and it becomes expensive for the consumers to run the service.
Malicious Insiders
Malicious Insiders can be a current or former employee, a contractor, or a business partner who gains access to a network, system, or data for malicious purposes. In an improperly designed cloud scenario, a malicious insider can wreak even greater havoc. From IaaS to PaaS to SaaS, the malicious insider has increasing levels of access to more critical systems and eventually to data. In situations where a cloud service provider is solely responsible for security, the risk is high.
Cloud Abuse
An example of cloud abuse is a bad guy using a cloud service to break an encryption key too difficult to crack on a standard computer. Another example might be a malicious hacker using cloud servers to launch a DoS attack, propagate malware, or share pirated software. The challenge here is for cloud providers to define what constitutes abuse and determine the best processes to identify it.
Insufficient Due Diligence
Organizations embrace the cloud without fully understanding the cloud environment and associated risks. For example, entering the cloud can generate contractual issues with providers over liability and transparency. What’s more, operational and architectural issues can arise if a company’s development team isn’t sufficiently familiar with cloud technologies as it pushes an app to the cloud. CSA’s basic advice for organizations is to make sure they have sufficient resources and to perform extensive due diligence before jumping into the cloud.
Pegged Shared Technology Vulnerabilities
Cloud service providers share infrastructure, platforms, and applications to deliver their services in a scalable way. According to the “The Notorious Nine” report “Whether it’s the underlying components that make up this infrastructure (for example, CPU caches and GPUs) that were not designed to offer strong isolation properties for a multi-tenant architecture (IaaS), redeployable platforms (PaaS), or multi-customer applications (SaaS), the threat of shared vulnerabilities exist in all delivery models”.
Courses to help you get
results with Cloud
Professional Cloud Solutions Architect™
The industry-recognized CCC Professional Cloud Solutions Architect™ certification is based on the Cloud standards developed by NIST and aims to empower you to design the future generation of technology solutions. A great understanding of the most important technologies, platforms, and Cloud standards is provided via hands-on, practical exercises, and case studies. The purpose is to…
Never miss an interesting article
Get our latest news, tutorials, guides, tips & deals delivered to your inbox.
Keep learning